In the world of VPN services, IPSec VPN is a phrase one is bound to encounter sooner than later. Simply put, IPSec is one of the most famous protocols used to enable VPN services. Some of the other names that you may have already heard include SSL, TLS, SSH, and more recent incarnations like OpenVPN, SSTL, and L2TP.
The Basics of IPSec VPN
The popularity of the IPSec protocol (or Internet Protocol Security) lies in the fact that it is the most accessible option when authenticating and encrypting data packages within a communication channel. Many VPN brands rely on IPSec to ensure that both ends of the communication stream recognize each other before data is being transmitted. For example, a user on VPN requesting data from the host or server has to use IPSec VPN to be able to establish the connection. Only after the authenticating process is complete will the request go through.
Once this is done, the next function of encrypting is enabled by the IPSec platform. The connection allows that the user and host can now talk in a common language, typically in a complex encryption algorithm which when intercepted cannot be decoded by the hacker. The two layers of protection – authentication and encryption – form the central foundation for VPN services and is responsible for the growth and evolution of newer forms of protection services today. Still, there is no doubt that the IPSec VPN protocol continues to hold significant sway in the internet security realm and is still heavily relied on when communicating sensitive data across unsecured networks.
Using IPSec VPN Services
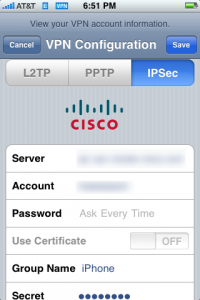
If you want to use IPSec VPN in your everyday transactions, all that you need to do is sign up with VPN brands that offer IPSec protocols in their options. These VPN brands are specifically designed for ease-of-use by most consumers so signing up to the VPN brand, in most cases, already enables the IPSec protection automatically. In other cases, installing a client may be necessary to enable the VPN protection. Regardless of whichever scenario is chosen, the IPSec protocol does its job by automatically managing authentication and encryption transactions between the user and the server. Whether you are using mobile internet devices, standard laptops, or even desktops, IPSec VPN will make sure that every data transmitted and received is safe and free from risks associated with unsecured networks.
For a small fee, you can reap the benefits of using a secure IPSec VPN system that is easy to use, relatively cheap, and highly reliable when it comes to data security and connectivity applications.
The Best IPSec VPN Options
The following VPN service listings all employ IPSec VPN protocols which can be manually enabled or automatically used as an authentication and encryption client when the VPN service is used. Check out the detailed reviews about each of these VPN products before choosing the one that fits your security and internet usage goals.

